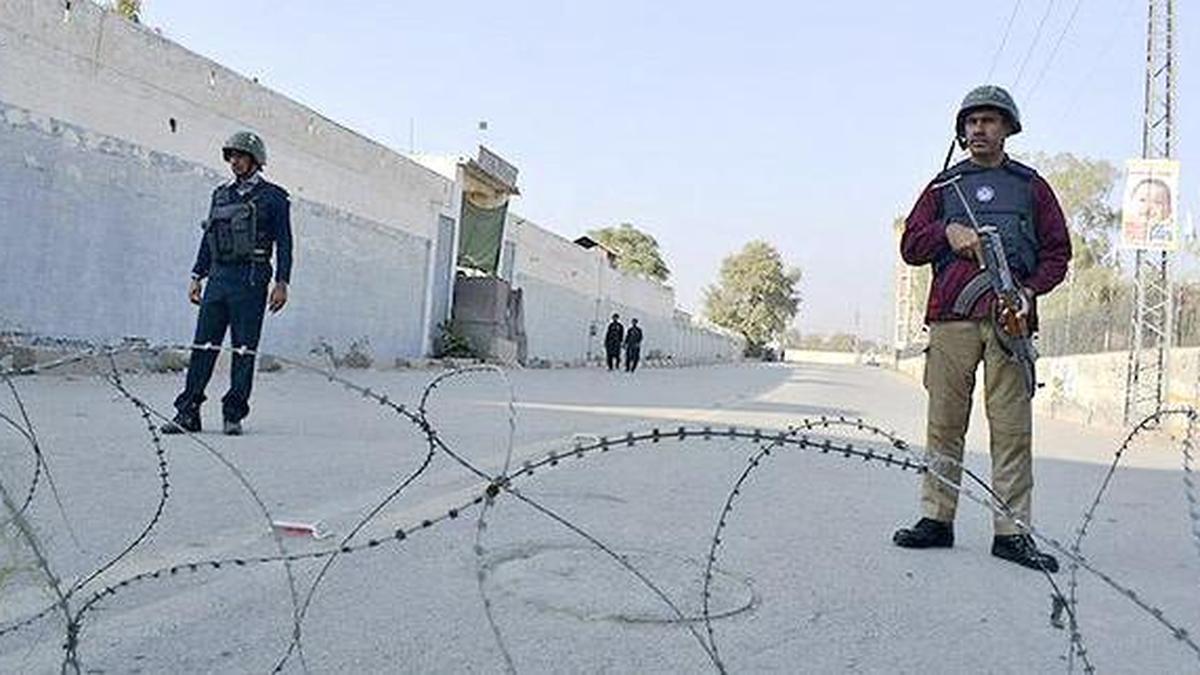
The kinetic engagement in Pakistan’s northwestern Bajaur district highlights a systemic tactical vulnerability within the state's border containment architecture. The incident, which resulted in the confirmed deaths of multiple state security personnel and at least nine militants associated with the Tehreek-e-Taliban Pakistan (TTP), demonstrates a clear evolution in asymmetric assault mechanics. Rather than proving a simple, isolated skirmish, the operation underscores how non-state actors exploit geographic and technological asymmetries to inflict disproportionate costs on stationary military positions.
The systemic deterioration of security in the Khyber Pakhtunkhwa province is measurable. Annual data indicates an escalation in total security-related fatalities from 1,620 to 2,331 over a twelve-month period—a 43.8% net increase in lethality. To analyze how small, mobile networks consistently compromise hardened state infrastructure, the threat must be modeled across three structural operational vectors: asymmetric technology integration, structural perimeter degradation, and cross-border geographic leverage.
The Asymmetric Tactic Matrix
The assault on the Bajaur scouts camp departed from historical small-arms ambush paradigms. It relied on a multi-tiered tactical framework designed to systematically strip the garrison of its defensive advantages before deploying ground forces.
The operation moved through three distinct phases:
- Aerial Surveillance and Initial Kinetic Disruption: The utilization of quadcopter unmanned aerial vehicles (UAVs) to establish real-time reconnaissance and conduct initial drops. This disrupted open-air perimeter defense and forced personnel into static, covered positions.
- Kinetic Breach via VBIED: The deployment of a Vehicle-Borne Improvised Explosive Device (VBIED) targeting the primary access node. The objective of a VBIED in this context is not merely lethal output; it serves as a kinetic breaching tool to neutralize structural barriers, destroy defensive gates, and induce sensory and organizational disorientation within the compound.
- Infiltration and Fire Overmatch: The immediate insertion of an armed assault element using small and medium automatic weapons into the breached perimeter. This phase exploits the structural gap and the temporary collapse of the garrison's command and control.
This combination creates a severe defensive bottleneck. State forces are forced to pivot instantly from an anti-aerial posture to an anti-armor, vehicle-interdiction posture, followed immediately by close-quarters urban combat. The structural damage—evident in the total collapse of masonry and the charring of central administrative structures—reveals that the TTP's offensive capability can reliably generate fire overmatch against isolated outposts before reinforcements can arrive.
The Friction of Frontier Geography
The persistence of this insurgent capacity depends directly on the structural realities of the Durand Line. The border presents a complex terrain matrix that heavily favors mobile, non-state actors over conventional military logistics.
[Militant Safe Havens / Rear Guard] ---> (Porous Mountain Frontier) ---> [Targeted Static Outpost]
|
[State Logistic Base] ---------------> (Delayed Mountain Corridor) --------------->+
The first limitation of conventional defense in Bajaur is the friction of response time. Mountainous terrain restricts the deployment of heavy armor and fast-moving ground reinforcements. Consequently, isolated garrisons function as strategic islands. The terrain acts as a natural dampener on state reinforcement velocity, guaranteeing that any assault element will enjoy a prolonged window of localized numerical and tactical superiority.
The second structural bottleneck is the porous nature of the frontier. The border enables low-signature, cross-border movement while acting as a shield against state pursuit. The TTP exploits this asymmetric geography by maintaining strategic depth and command infrastructure in contiguous territory, while executing high-intensity, short-duration kinetic operations within Pakistan. The state’s defensive posture remains structurally reactive; it is forced to secure thousands of potential vector points along a complex perimeter with a finite number of static assets.
The Attrition Balance Sheet
To evaluate the strategic efficacy of these engagements, analysts must look past basic casualty ratios. In conventional warfare, a 9:4 or 9:8 kill ratio in favor of the defending force might suggest a successful defense. In an asymmetric war of attrition, this calculation is fundamentally flawed.
The cost function favors the insurgent network across three primary metrics:
- Asset Replacement Ratios: Non-state actors recruit from a highly motivated, low-overhead labor pool. The cost to train, equip, and deploy a militant foot soldier is orders of magnitude lower than the cost to train, sustain, and replace a professional state security officer or border scout.
- Capital Asymmetry: The economic expenditure required to build, fortify, supply, and staff a remote border outpost represents a permanent drain on state capital. Conversely, the offensive apparatus requires minimal capital output—primarily commercial quadcopters, improvised explosives, and legacy small arms.
- Information Velocity: Insurgent groups operate with decentralized command structures, enabling rapid adaptation to local tactical failures. The state military apparatus operates under rigid, bureaucratic hierarchies, creating a lag between tactical evolution on the border and strategic procurement or doctrinal shifts at headquarters.
This dynamic creates a structural deficit for state forces. Every successful breach of a border outpost degrades local intelligence networks, damages state prestige, and forces the military to reallocate scarce resources from proactive counter-insurgency operations to reactive, static base hardening.
Force-Protection Recommendations
Defending static border installations against multi-vector, technology-enabled assaults requires a fundamental pivot from passive structural defense to active, automated denial frameworks.
State forces must systematically replace personnel-heavy perimeter security with automated electronic counter-measures. Deploying localized, automated radio-frequency jamming networks and directed-energy counter-UAV systems at the outer perimeter is required to neutralize the aerial reconnaissance vector before an assault begins.
Furthermore, structural access points must be engineered with deep, non-linear vehicle-interdiction chicanes and reinforced anti-ram barriers located well outside the compound’s primary blast walls. This displaces the detonation point of a VBIED, preserving the structural integrity of the main garrison buildings and preventing the immediate entry of secondary infantry assault teams.
Finally, strategic doctrine must shift from static territorial holding actions to highly mobile, heliborne rapid-reaction forces capable of projecting air-delivered fire overmatch within minutes of a perimeter breach. Without these proactive upgrades, isolated border outposts will remain highly vulnerable to the evolving tactical combination of commercial drone technology and heavy explosive breaching vehicles.